Cloud-native TI: why C5 and Confidential Computing actually matter
"Cloud-native" has become a comfortable phrase in TI conversations. But for anyone who has actually shipped a TI-adjacent cloud workload, it's the opposite of comfortable: it means navigating a stack of security, compliance, and certification requirements that were written long before cloud was the default.
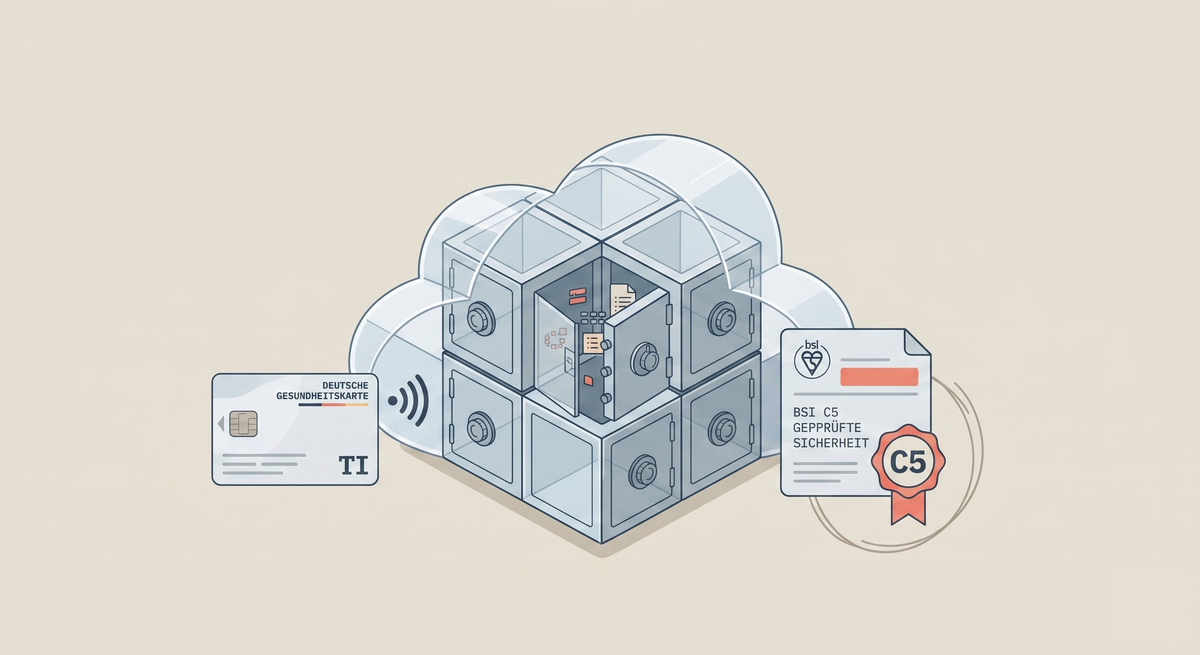
Three of those layers do most of the heavy lifting — BSI certification, C5 compliance, and Confidential Computing. They're worth understanding on their own terms.
BSI certification experience
The Bundesamt für Sicherheit in der Informationstechnik (BSI) is the gatekeeper for any component that wants to live inside the German Telematikinfrastruktur. Getting a component approved isn't a form to fill out — it's a structured engagement that touches architecture, cryptography, operational controls, and documentation.
What matters in practice isn't "have you read the BSI catalogue" but "have you been through the process, survived the findings, and come out with something in production". That's the experience we've built operating infrastructure in the TI ecosystem — and it's what lets us architect new components in a way that won't bounce off a certification review six months in.
C5-certified environments
C5 — the Cloud Computing Compliance Controls Catalogue — is BSI's framework for evaluating cloud services against a harmonised set of security controls. For anything touching healthcare data, C5 isn't a nice-to-have; it's the baseline that makes a cloud environment defensible to regulators, customers, and internal security teams.
Operating a C5-certified environment shapes how you build: logging, access controls, change management, incident response, supply-chain transparency — all of it gets audited on a cadence. We run C5-compliant environments for our Healthcare Confidential Computing (HCC) workloads; the compliance posture is part of the product, not a sticker on it.
Confidential Computing as the security floor
Most cloud security stops at "data at rest is encrypted, data in transit is encrypted". Confidential Computing closes the gap at the third boundary: data in use. Workloads run inside hardware-enforced enclaves, so even the cloud operator cannot read the memory of the process.
For healthcare workloads this changes the trust model. A PVS vendor or a Krankenkasse considering a cloud-based TI component no longer has to trust the cloud provider's operators not to snoop — the hardware enforces it. It's the difference between "we promise we won't look" and "we cannot look". That distinction is what makes cloud-native TI credible to security teams who have historically rejected any cloud at all.
Why all three together
None of these layers is enough on its own. BSI certification without operational maturity is a paper exercise. C5 without Confidential Computing leaves the "data in use" gap open. Confidential Computing without certification coverage is a technology without an audit trail.
Cloud-native TI works when the three reinforce each other — and that's the posture we build from.
Talk to us if you're evaluating a cloud-native TI path, or if you're stuck in a certification loop that shouldn't be this hard.